Digital signature is the way any document or message can be added with a proof that document is really coming from the sender and has not being tampered in the meantime. This can be verified using the public key of the sender and if verification is fine, then there is no doubt that the signature was created using the private key belonging uniquely to the sender.
So the digital signature can
- prove that the message was not changed (integrity);
- prove the source of the message (authentication);
- make sure that the digital signature is not fake, in such a way that the signer cannot deny having sent the message later on (non-repudiation);
The digital signature is made by the private key of the sender (or signer). Digital signature uses asymmetric cryptography. The following details are valid:
- the document does not need to be encrypted;
- nobody else can sign, because only the sender has the private key;
- any change in the message (or document) will invalidate the signature;
- to verify the digital signature the corresponding public key is needed;
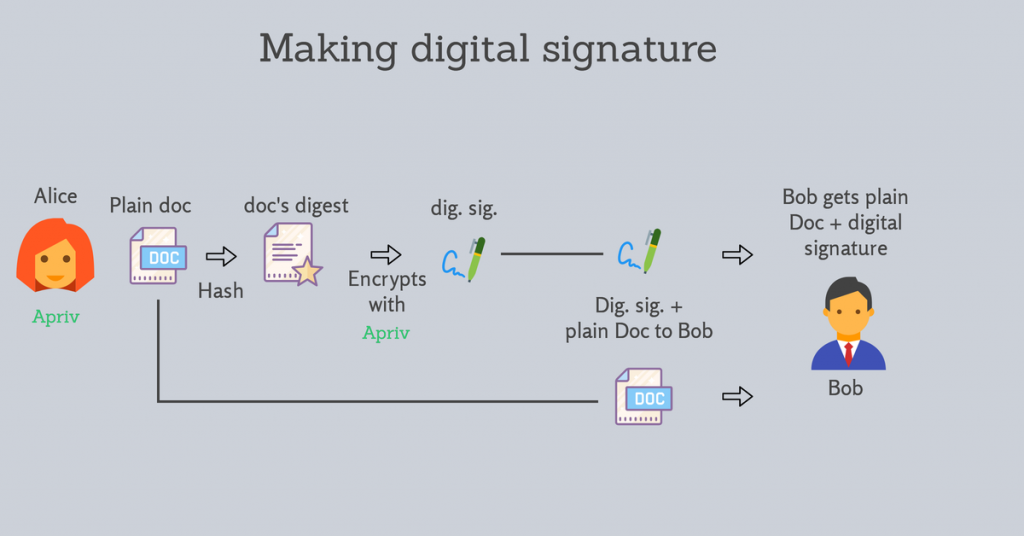
How the sender makes the digital signature
Let’s see, step by step, how the procedure of making a digital signature is done using the sender’s private key:
- Alice wants to send a plain document to Bob and wants to sign such a way that Bob is sure that is coming from Alice and no one has tampered it while coming to him;
- Alice created the hash of the document using an hashing function. The result is named also “document’s or message’s digest”;
- The document’s digest is encrypted with Alice’s private key. This is called “digital signature” of such a document;
- The plain document is sent along with the digital signature to Bob;
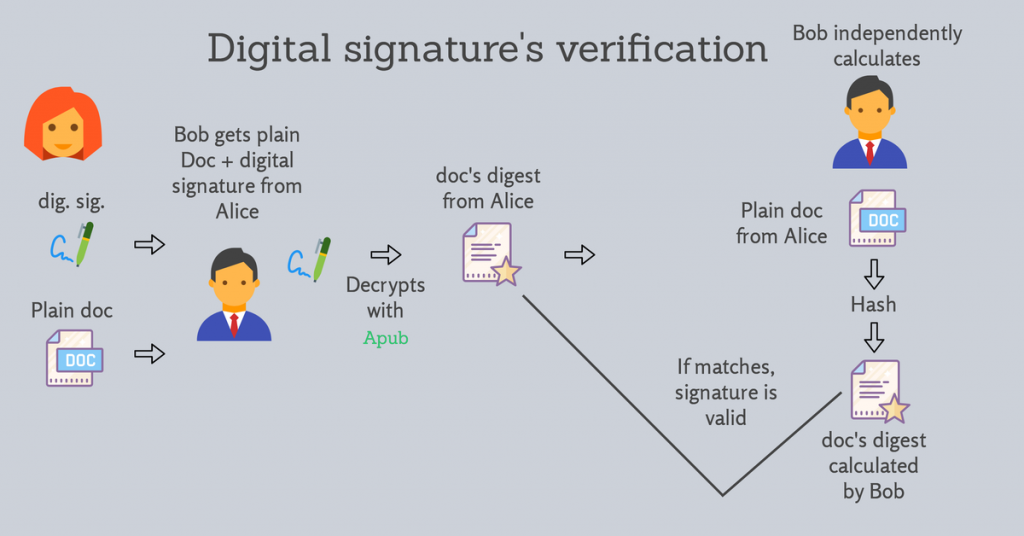
How the received verifies the digital signature
Now we are going to see how Bob can receive the document and check that the digital signature belongs really to Alice and the document has not being tampered:
- Bob gets both digital signature and plain document;
- Bob uses Alice’s public key to decrypt the digital signature and therefore gets the document’s digest as sent by Alice;
- Bob takes the plain document and calculates by himself the document’s digest using the same hashing algorithm;
- Finally Bob checks if the document’s digest calculated independently is matching the digest from Alice (as previously decrypted using Alice’s public key);
- If the digest matches, then there is no doubt the signature is genuine and only the owner of the corresponding private key could create it: Alice.
This procedure is very important today and used in many procedures and technologies. So understanding is a key value for all.